New Linux “Dirty Frag” Vulnerability Could Give Attackers Root Access
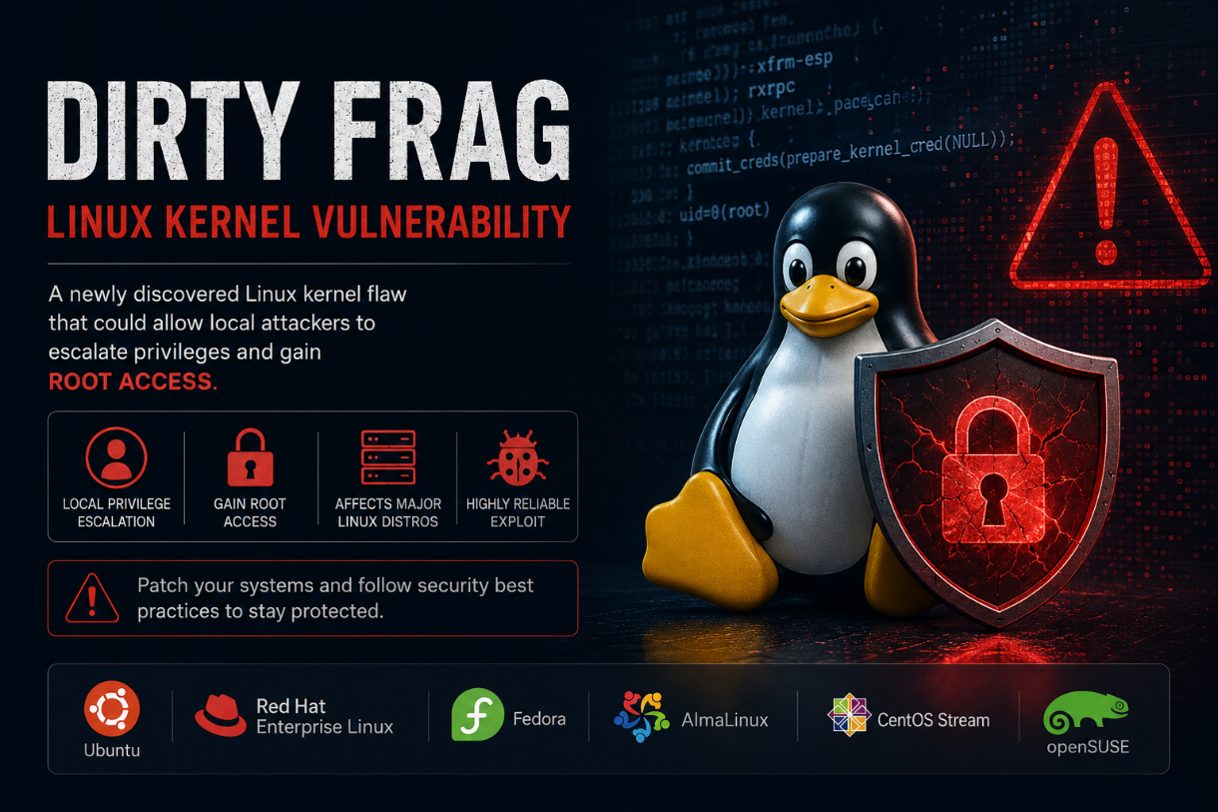
A newly discovered Linux kernel vulnerability called “Dirty Frag” is raising concerns across the cybersecurity community because it can allow attackers to gain full administrator, or “root,” access on affected Linux systems. Security researchers say the issue impacts many major Linux distributions and can be exploited with a very high success rate.
What Is Dirty Frag?
Dirty Frag is a local privilege escalation vulnerability. That means an attacker first needs some level of access to a Linux system, such as a compromised user account, remote shell access, or access gained through another vulnerability. Once inside, they may be able to elevate their permissions and take full control of the machine.
Researchers describe Dirty Frag as similar to previous Linux vulnerabilities such as Dirty Pipe and Copy Fail. The flaw works by abusing weaknesses in how the Linux kernel handles memory and page-cache operations.
What makes Dirty Frag especially dangerous is that it reportedly does not rely on unstable timing attacks or race conditions. According to researchers, the exploit is highly reliable and can work consistently across multiple Linux distributions.
Which Systems Are Affected?
Reports indicate the vulnerability affects a wide range of Linux environments, including:
- Ubuntu
- Red Hat Enterprise Linux (RHEL)
- Fedora
- AlmaLinux
- CentOS Stream
- openSUSE
Several kernel components are involved, including the xfrm-ESP and RxRPC subsystems. One of the vulnerabilities tied to Dirty Frag has already received a CVE identifier, while another issue is still awaiting a full patch.
Why This Matters for Businesses
Linux powers a large percentage of servers, cloud infrastructure, web hosting platforms, and enterprise systems worldwide. If attackers gain root access, they can:
- Install malware or ransomware
- Steal sensitive business data
- Create hidden backdoors
- Disable security tools
- Move deeper into a company network
- Escape from containers in some cloud environments
Security researchers also warned that containerized workloads could face additional risks if the vulnerability is exploited inside shared hosting or Kubernetes environments.
Is There a Patch Available?
At the time of reporting, one part of the vulnerability chain has been patched in the Linux kernel mainline, while another component still does not have a complete fix available.
Linux vendors are expected to continue releasing security updates as patches become available. Organizations running Linux servers should monitor vendor advisories closely and apply updates as soon as possible.
Recommended Mitigation Steps
Until all fixes are available and installed, organizations should consider taking the following precautions:
- Update Linux systems immediately when patches are released
- Restrict local user access where possible
- Monitor systems for unusual privilege escalation activity
- Disable unnecessary kernel modules if recommended by vendors
- Review container and cloud security configurations
- Use endpoint detection and monitoring tools to identify suspicious behavior
Researchers also published temporary mitigation guidance involving disabling certain vulnerable kernel modules.
Final Thoughts
The Dirty Frag vulnerability is another reminder that even widely trusted operating systems like Linux require constant monitoring and patch management. While the exploit requires local access, attackers frequently combine privilege escalation flaws with phishing attacks, stolen credentials, or other vulnerabilities to fully compromise systems.
Businesses using Linux servers, cloud workloads, or container environments should prioritize patching and review their security posture immediately.
Cybersecurity threats continue to evolve rapidly, and proactive system maintenance remains one of the best defenses against emerging attacks.